Regent University Hosts Inaugural Cybersecurity Summit

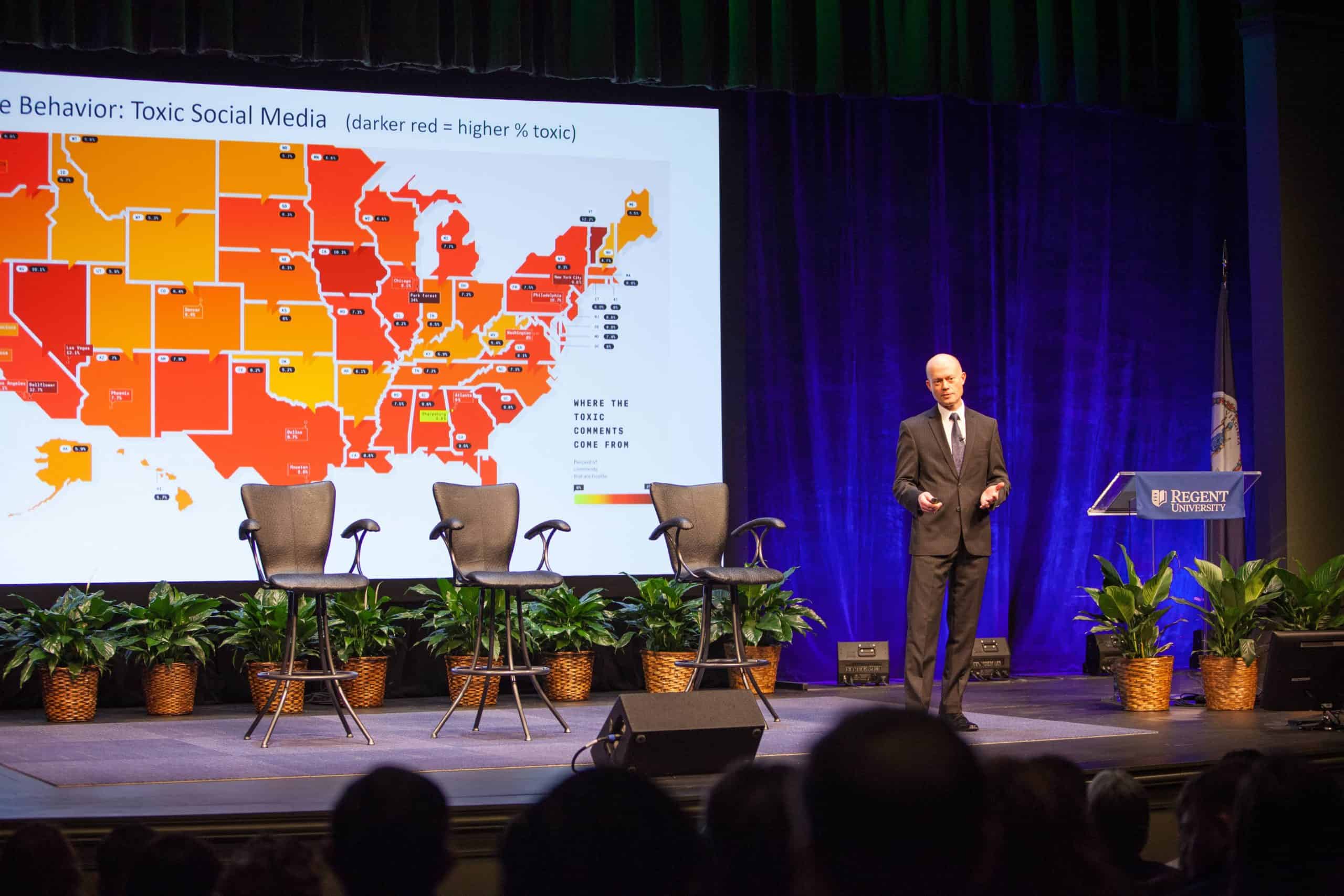
On Thursday, February 15, Regent University’s inaugural Cybersecurity Summit generated a wide-ranging discussion about current and future security concerns facing businesses, government, healthcare organizations and consumers as the world increasingly relies on interactive devices for productivity and convenience.
“These issues are of great concern to all of us,” said summit moderator Dr. Gerson Moreno-Riaño, Regent’s executive vice president for Academic Affairs, as he set a sobering tone for the more than 500 students and community and business leaders who attended the summit at the university’s performing arts center.
An assortment of experts followed Moreno-Riaño, warning that the continued growth in the types and uses of interactive devices will open more potential threats to national, corporate, community and personal security. Speakers and panelists offered suggestions for heading off or quickly resolving cyber-based havoc, but noted the need for a more well-trained and ethically steeped cyber workforce.
“There’s a major skills shortage in this industry. According to recent research, 51 percent of organizations said they had a major problematic skills shortage and this is only getting worse,” said Ian Green, who helps manage the detection and response team for Google. “Even organizations with well-stocked cybersecurity teams, such as my own, are struggling to keep up with the demands of an ever increasingly connected world.”
He added: “We need a higher level of skilled labor. … That’s the only way we’re going to be able to tackle these problems.”
Some speakers suggested ideas for shaping employee teams for quicker response to cyber threats, but the discussion often returned to how to find the best job candidates. Brian DeMuth, chief executive officer of GRIMM, an engineering and consulting firm, said companies should look beyond traditional resume information to determine a job seeker’s analytical ability and passion for solving problems.
Still, DeMuth expressed concern that new generations of bright cyber employees need to shore up their experience in actually detecting criminal and other malicious threats.
Experts forecast 6 million cybersecurity jobs by 2019; and Regent is preparing students to help meet the needs. The university offers an array of on-campus and online degrees and certificates in cyber and digital forensics, cybersecurity, information systems technology and computer science. In October 2017, Regent launched its Cyber Range training center, a world-class facility that will enable training for and simulation of real-time attacks and security breaches.
The need to thwart attacks and breaches is only going to grow, said Roy Zur, founder and CEO of Cybint, who headed the discussion on “The Cyber Safe City of the Future.”
A retired major from the Israeli military, Zur noted that more cities not only provide free Wi-Fi but also devise greater interactivity in basic urban services, such as policing, transportation and traffic flow, water and sewage systems, and waste management. All will have the potential to be targeted by hackers seeking to do mischief or physical harm or to gain access to confidential information about employees and taxpayers.
“Smart cities are great things,” but the sensors and other high-tech equipment that control municipal services “could be used against us” if not adequately secured, Zur warned. He urged cities to develop “cyber resilience plans” for the prevention, detection and remediation of breaches and attacks. Additional solutions, he said, should involve greater collaboration and sharing of attack-prevention information among various levels of government.
Consumers also have roles in cybersecurity, advised panelists Robert R. Cochran, an FBI expert in cyber crimes, and Jon Green, vice president and chief technologist for Aruba, a Hewlett Packard Enterprise company.
“Some hings are better left mechanized” instead of computerized, Cochran said. “Not everything needs to be ‘smart.’ Tell me why your refrigerator needs an internet connection.”
Green said he recently counted 87 interactive devices in his household, including his daughter’s dollhouse, and warned that cybersecurity problems could be never-ending if consumers aren’t careful with such possessions.
Zur and Green also urged manufacturers to develop security assurance protocols when designing, developing and testing products, just as they have long done with quality assurance.
Several speakers discussed how hackers can help improve security. For example, some hackers are not aiming to cause problems but are trying to help point out product flaws that could be open to attacks. Speakers also pointed out the need to carefully vet vendors and suppliers, including the sources of any equipment they might use, so they don’t inadvertently bring in malware or similar invasive technology.
Manufacturers of medical equipment are concerned about the vulnerability of sophisticated devices that are being developed for embedding into patients with serious health conditions, said Steve Abrahamson, senior director of product security for GE Healthcare. “One of the frightening things is that bad actors can do things remotely,” he said. “Theoretically, it’s possible to hack into medical devices, (but) we haven’t seen it yet.”
Concerns, he said, include the potential for disrupting the rhythm of heart pacemakers or stopping them entirely. Other types of cyber breaches, he said, involve breaching patient records with the intent of stealing confidential information or committing fraud, all of which already is happening.
“This is not science fiction. This is not far-fetched,” said Dr. Deva Henry, assistant professor of engineering and computer science at Regent. He asserted that the work to prevent ill-intended hacks must start even before new products are designed.
Dr. Richard V. Homan, president and provost of Eastern Virginia Medical School in Norfolk, encouraged corporations and institutions to weigh the trade-offs when trying to balance potentially competing concerns, such as patient safety, confidentiality and costs.
Increased potential for cyberhacking should prompt businesses to reconsider the tasks of leaders and the training of employees, according to Ryan Leirvik, chief operating officer of GRIMM. He advised that corporations undertake studies to understand their risks, manage their risks and measure their risks.
Dr. Mary Manjikian, a Regent professor of government, injected the issue of ethics into the summit. “The best way to get people to think about ethics,” she said, “is to get them to think about ethics early.”
The Cybersecurity Summit was presented by The Darwin Group LLC. Panel discussions were sponsored by Aruba: A Hewlett Packard Enterprise Company, and GRIMM.
Special thanks to Michael Knepler.