Information Security
The Information Technology department is committed to ensuring the privacy of your information during and after your tenure here at Regent. But we need your help. By staying up-to-date on the latest techniques for information security, you can protect yourself and others against fraud, theft, and worse.
Cybersecurity Awareness is an important skill required for every member of a modern organization.
Regent University takes this responsibility seriously, and requires all Staff, Faculty, Adjuncts and Student Workers to participate in our Security Awareness Training Program.
Regent’s Security Awareness Training Program consists of two components: Training and Assessment.
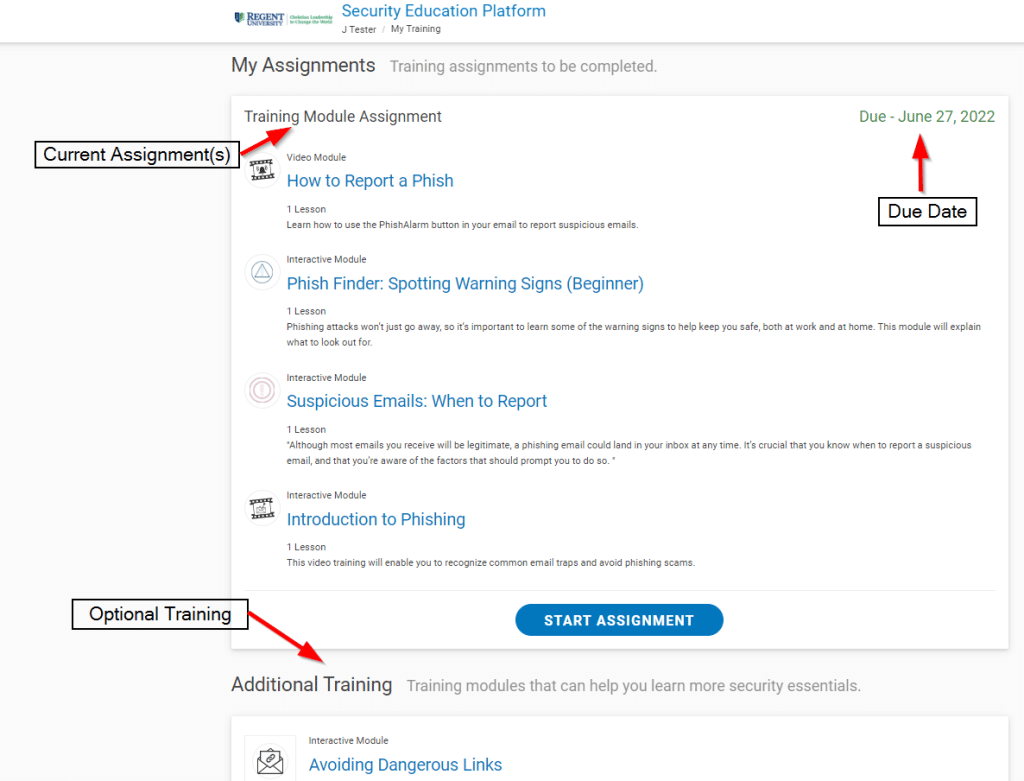
Periodic and targeted training will be assigned on a regular basis.
Training assignments will cover basic Information Security topics for defense and topical alerts about recently seen scams and malicious tactics. Training assignments are designed to take under 30 minutes.
Remedial training may also be assigned to individuals needing a refresher course on Email and Information Security best practices.
Optional training topics are also available within the Security Awareness Program for anyone interested.
Communication
Security Awareness Training program invites will look like this:
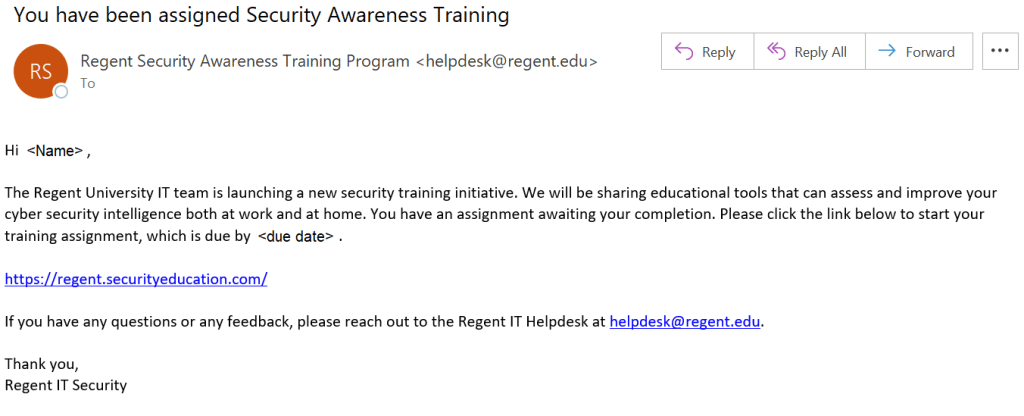
Reminders may be sent from the same address (“Regent Security Awareness Training” <helpdesk@regent.edu>).
All assigned training can be accessed here: https://regent.securityeducation.com.
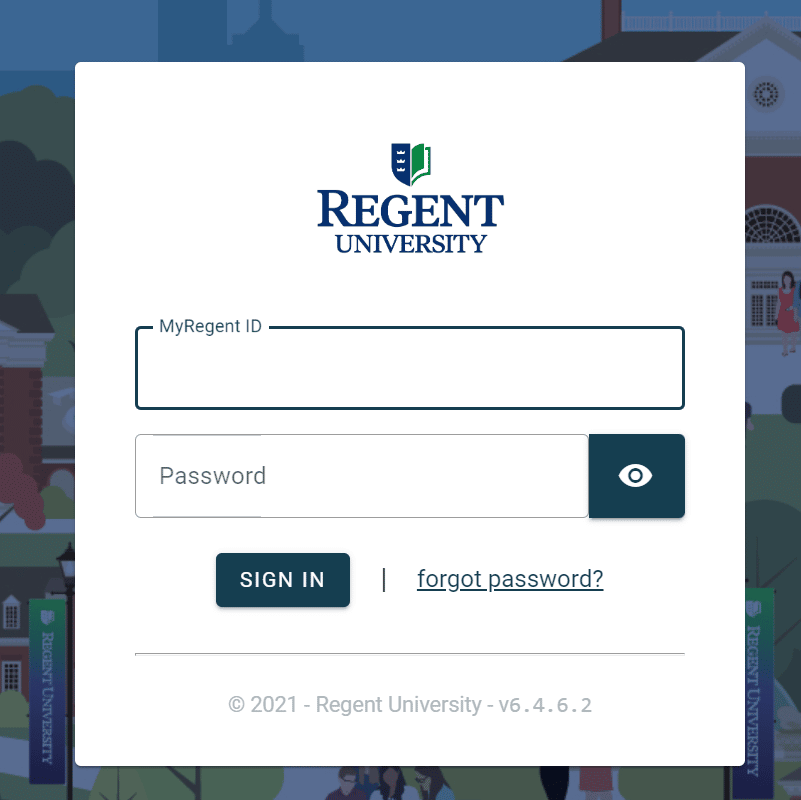
Please expect to be prompted for the standard Regent University Single Sign-On page as shown below.
The training portal will appear as follows:
As part of the Security Awareness program focused on Email Phishing attempts, mock phishing messages may be sent at any time to assess individual awareness.
The included training will help you identify suspicious or potential phishing messages.
When you think you have found a phishing email, simply use the “Report Phish” button included in Outlook to report it.
Program Requirement
Privacy and Security are no longer an option in our educational system. Security Awareness is essential for everyone’s work habits, both on and off-campus. Regent University is required by several of our accreditation and auditing bodies to have an annually audited Security Awareness Training program with full participation. This program is mandatory.
In simplest terms, Password Security is the process of choosing a difficult to guess password, then keeping it a secret. Since your password/s are the primary protection mechanism for your accounts, a poorly chosen (weak) password may result in compromise of personal user information and possibly confidential Regent University information. As such, all Regent University faculty, staff, and students (including visitors, contractors, and vendors with access to Regent University systems) are responsible for taking appropriate measures to select and secure their passwords.
Attackers can use programs to compromise easily guessed passwords. When an attacker has access to your accounts, then he/she may inherit access to your private information and/or confidential Regent University information. Because of this, the IT department has adopted more strenuous password complexity requirements. Your new password will make it more difficult for an attacker to compromise your accounts. Remember, your password can be super difficult to guess, but if you share it with anyone, you’ve already compromised your accounts. So choose a difficult to guess password, then keep it a secret.
At Regent, we now have a few new requirements to make sure that our users create what we call ‘Strong Passwords’. These are passwords that an imposter could not easily crack. Your new password must:
- Be at least fourteen (14) characters in length
- Contains at least one upper case letter (A-Z)
- Contains at least one lower case letter (a-z)
- Contains at least one number (0-9)
- Contains at least one special character (!*-._+:?[\]^~)
- Be different than your other passwords
- Not be based on personal information, names of family, etc.
A good way to create a strong password is by using a ‘Pass Phrase’. These use something that you can easily remember, such as a Bible verse or song lyric, instead of a random string of characters. Pass phrases are typically stronger and easier to remember than a traditional password. Take the following example for instance.
Phrase: “Regent University, Christian Leadership to Change the World!”
We could certainly break this phrase up or use the whole phrase to create a strong password. For this example, let’s use part of the phrase along with numeric and special characters to meet the complexity requirement.
Christian-Leadership-2-Change-the-World!
Great! It meets all of our requirements. It has at least fourteen characters, upper and lowercase letters, a number, and special characters. Here are some other examples of strong passwords formed from phrases:
Phrase: “John 3:16, For God so Loved the World”
Possible Passwords:
4_God_so_Loved_the_World
John+3:16+For+God+so+Loved+the+World
God^so^Loved<3the^World
Phrase: “Peas and Carrots”
Possible Passwords:
P3as[and]C4rrots
Pea5+and+Carr0ts
8Peas~AND~2Carrots
In each of these examples, the chosen passwords meet the University guidelines for minimum password criteria. Also, each password is not based on any personal information.
Now pick a phrase for yourself. Maybe a Bible verse, famous quote, or anything you like. Remember, don’t use words or phrases that others may think you will use. Don’t make it easy for someone to guess your password!
Passwords are personal information that should never be shared with any other person, including, but not limited to, instructors, assistants, staff (including IT staff), or supervisors. You should never send passwords via email, as this is an insecure medium. You should avoid writing down passwords and/or storing them in an insecure place. You should also never store passwords in plaintext on your computer (in a file, document, excel sheet, etc.)
You SHOULD use a strong and unique password for every website and service that you use – this means that the password you use for your Regent ID should NOT be used anywhere else. This is especially true for free services, where a breach in their security can expose your credentials if you happened to sign up with your Regent email.
We recommend that you use a unique password for every site and service that you use, and to try and avoid using your Regent work email to sign up for personal services.
This adds up to a lot of passwords, and you should not be storing them in a local file or even letting your browser store your passwords for you.
What is a good way to handle all these passwords? A password manager. There are several free and paid options that use robust encryption so secure your entire password database with a single (strong) Master Password. There are locally-managed versions and cloud versions; generally the cloud version offers an easier-to-use experience as you do not need to worry about accessing your password database from wherever you happen to be.
As of Fall 2023, Regent IT recommends BitWarden as a solid peer-reviewed option. The free plan is more than sufficient for personal use.
Other options include:
LastPass used to be a strong contender, however a recent major breach has undermined their security reputation.
Just as your Regent ID is secured with 2 Factor Authentication, it is a good idea to secure your password manager database with a second factor.
Users should contact the Help Desk at 757.352.4076 or helpdesk@regent.edu if you forget your password. The Help Desk has the ability to reset your password to a temporary value.
NOTE: Regent IT will NEVER ask you to provide your password either over the phone or by email. Once given the temporary password, you should set a new strong password using the password reset page as soon as possible.
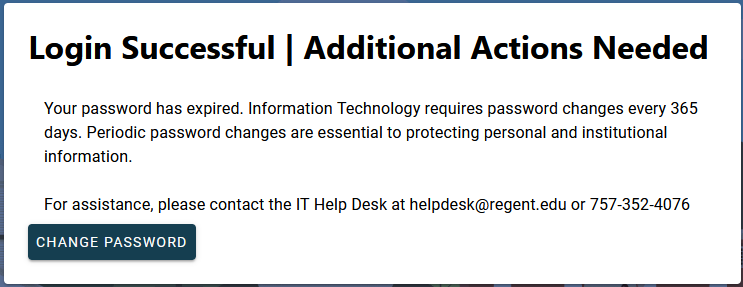
Regent University requires everyone to change their password at least once per year (365 days). If you have reached this limit you will see the following message when logging in to the MyRegent Portal:
If at any time you suspect that your password has been shared or compromised, you should immediately change that password anywhere it may have been used.
Our password change process will check each new password to make sure that it meets our new requirements. If it doesn’t, you’ll have to try again. To help reduce the chances of getting rejected, make sure that you’ve satisfied the following checklist.
- Understand why passwords and secrecy are important
- Understand which kinds of characters your password MUST include
- Understand which kinds of characters your password must NOT include
- Have chosen a good phrase to base your password on
- Make sure your password meets the complexity requirements
If you are ready to change your password, click here to start our three-step process.
Proofpoint Enterprise Protection
To help protect Regent University from email-based virus and phishing attacks and to protect you from receiving obnoxious spam messages, IT has implemented Proofpoint Enterprise Protection.
This system blocks messages with virus-infected attachments, scam or phishing content and obvious spam messages. The spam filtering is performed based on a confidence level, with the highest confidence spam automatically blocked.
Access the Proofpoint Digest »
Email with an uncertain spam confidence, including ads, newsletters and questionable email is quarantined separately for each user, viewable in your personal digest. Every week a personal digest is delivered listing details about the email in your quarantine (if your personal quarantine is empty no digest will be delivered). Actions can be taken based on the contents of this quarantine directly from the email digest, or from a web view. This can include adding senders to the safelist to bypass the quarantine and releasing messages to your inbox. If no action is taken on emails in the quarantine, the oldest messages are automatically purged.
The End User Digest is available in two ways, both will display your personal list of digest emails:
- Email Summary View. Send by email every Monday to your inbox from “Mail System Manger”.
- Digest Web View. Available at this link any time (also available from “Manage My Account link in the email summary.)
Email Summary View
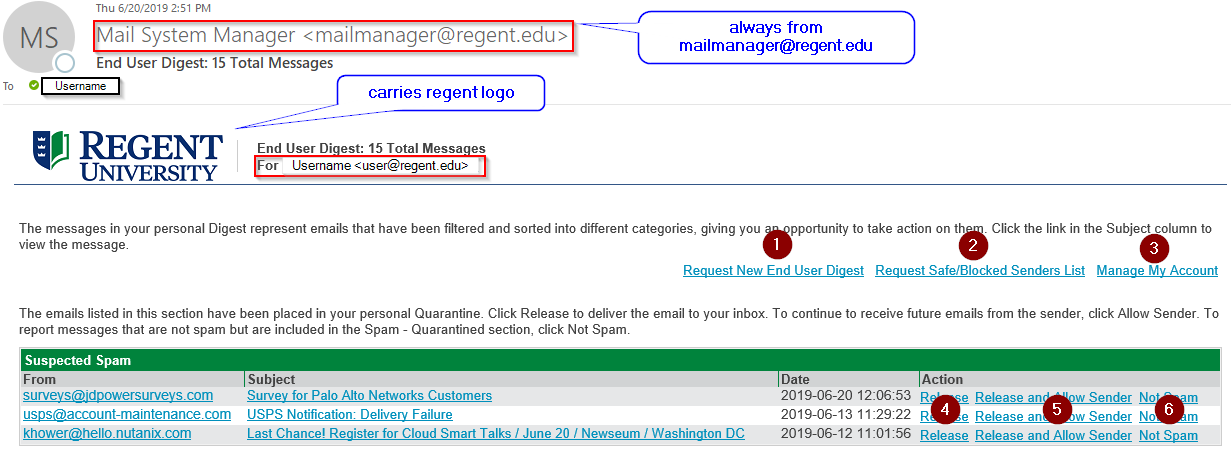
- Request New End User Digest. This link can be used from any previous digest email to request an updated digest delivered to your inbox on demand.
- Request Safe/Blocked Senders List. These lists can be defined in the Digest Web View. Note: As legitimate mail is unlikely to be quarantined and spam messages are automatically discarded from the quarantine after 4 weeks, the use of Safe/Blocked sender lists is generally not needed for most users.
- Manage My Account. This link will open the quarantine account page.
- Release. Use this link to release a message to your inbox. If you are unsure about the message you can preview in the web view by clicking on the subject.
- Release and Allow Sender. Use this link to release a message to your inbox and add the sender email address to your Safe Senders list.
- Not Spam. Use this link to report a potential false positive quarantine and request that the message be re-evaluated.
Digest Web View
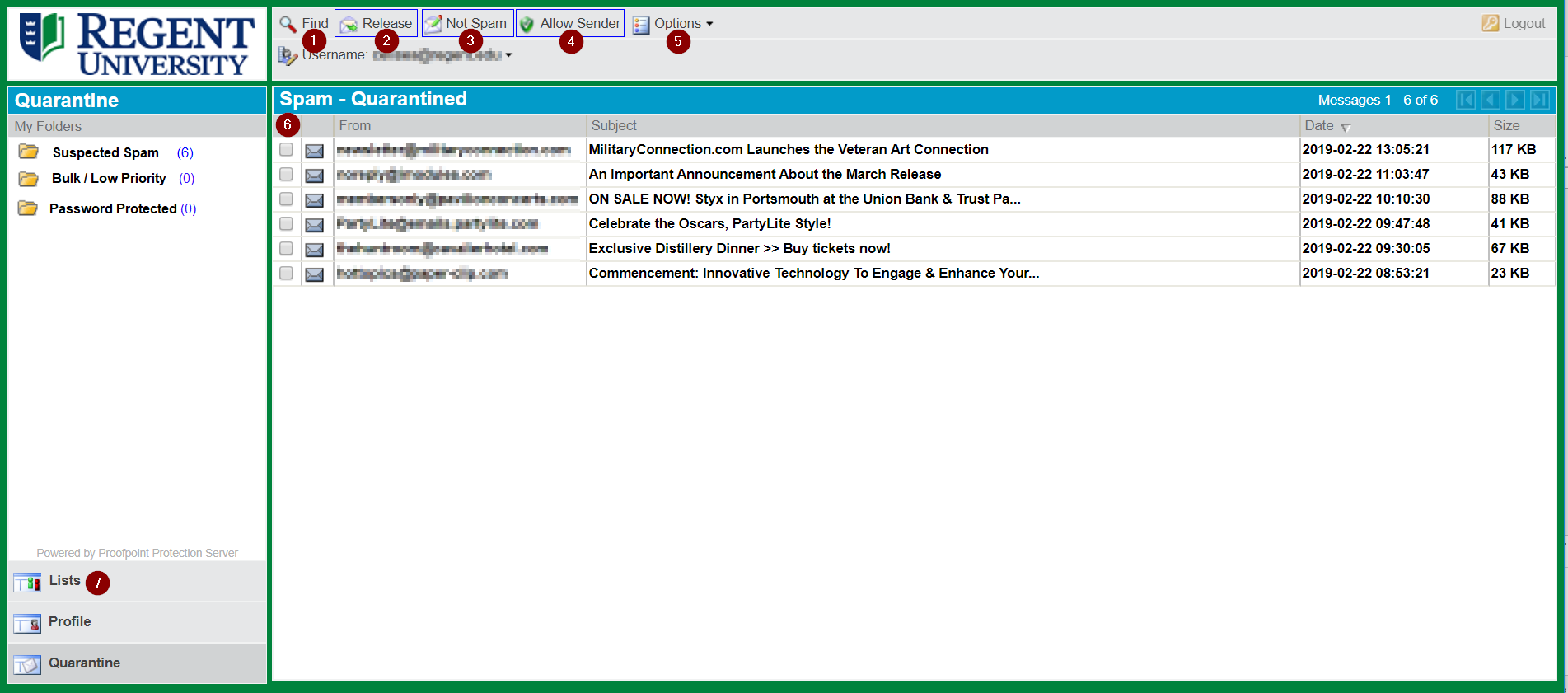
- Find. Search quarantined messages by sender, subject or date range.
- Release. As with the digest, releases messages to your inbox.
- Not Spam. As with the digest, requests that messages be reclassified.
- Allow Sender. As with the digest, adds the sender address to your Safe Senders list.
- Options. Selections for the following: Request a new Digest, Refresh the Quarantine list, Delete All messages from the quarantine.
- Check boxes – this allows the above actions to be taken on multiple emails at once.
- Lists:
- Safe Senders. Manually add email addresses here. Mail from these addresses will never be quarantined and will be delivered directly to your inbox.
- Blocked Senders. Manually add email addresses here. Mail from these addresses will always be quarantined. Note: Obvious spam and malicious mail will be blocked or quarantined automatically, so this list is only necessary for unwanted correspondence that is not being classified as spam.
- A primary way that malicious emails compromise security is by including one or more links to compromised websites. The links can perform several malicious actions:
- Directly download malware or tracking software. Clicking the link could redirect to a site that automatically starts a virus download.
- Link to a virus-infected site that runs malicious code directly from the browser
- Link to a fake login page that looks like a legitimate site in order to capture credentials. The site could look like a Microsoft login, a bank login or even a Regent login page.
- Proofpoint URL Defense offers protection against email URL attacks by scanning all emails and attachments for hyperlinks to potentially malicious sites. Links to known-good sites and internal sites are unchanged.
- For any unknown or potentially risky site, the link target is re-written with a Proofpoint proxy address. This address will be a long URL always starting with https://urldefense.proofpoint.com.
- All links that are re-written are scanned by Proofpoint for malicious or misleading content. If the site is clean, then the Proofpoint proxy address will re-direct to the original site and the link will work as normal to get to the intended site.
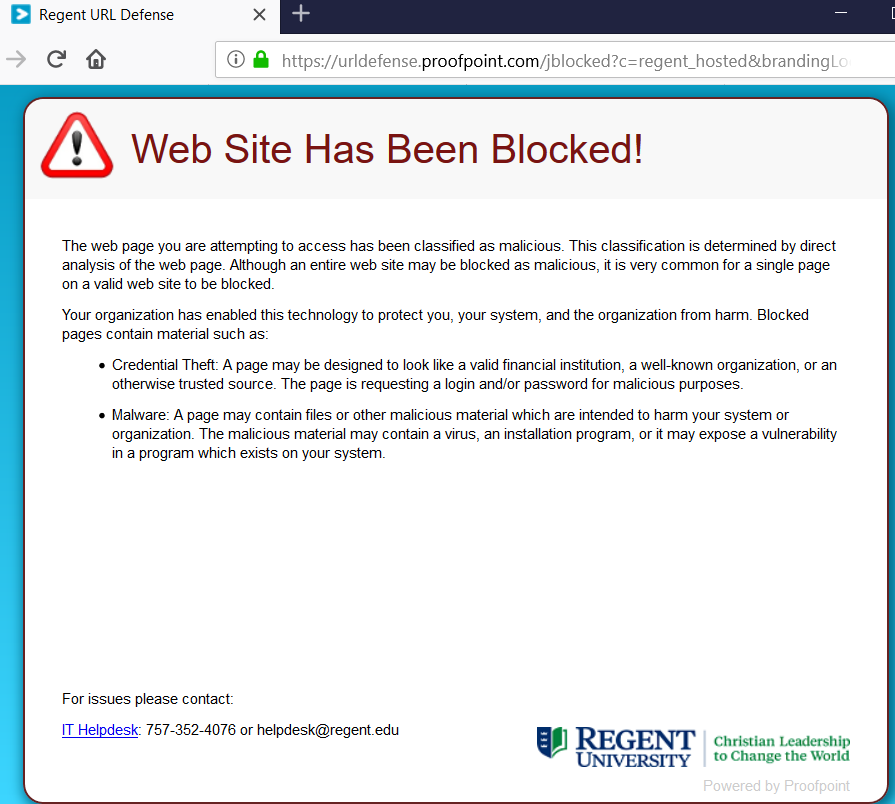
If the target site contains malicious, phishing or virus content then the Proofpoint proxy address will take you to a block page like the following:
Some examples of links using this feature
Example #1.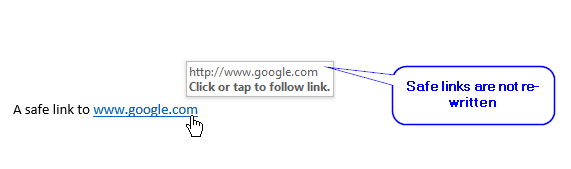
Example #2.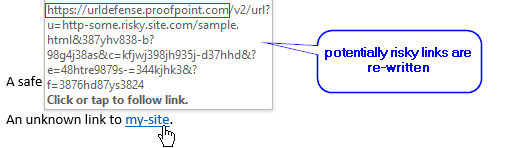
Example #3.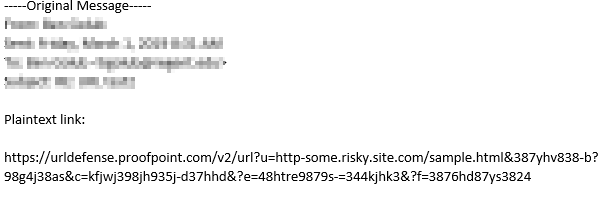
Example #4. Phishing message with re-write.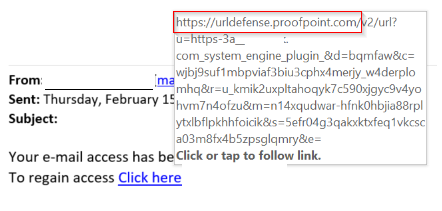
Usage
No additional action is needed to use this feature. Email security best practices should still be followed but this feature provides an extra line of defense when accidentally clicking on a potentially dangerous link.
*Note: if this feature impacts the operation of links to known safe sites, a ticket can be opened through the help desk to exclude them from URL defense.
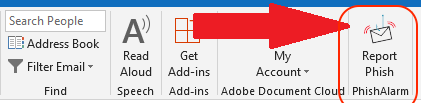

Regent University Email clients now have a single-click method to report suspicious emails. The email client add-in “PhishAlarm” button will automatically forward the selected email to the Regent IT team for review and analysis.
How it works
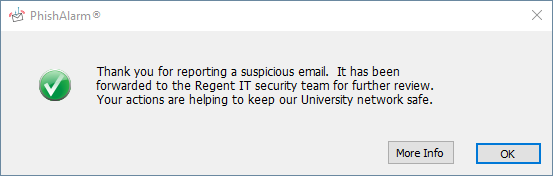
When you receive a suspicious looking email, either within the message preview pane or the opened message, click on the PhishAlarm button. You will receive immediate feedback via a pop-up window and the selected message will be moved to your “junk” or “spam” folder.
What to Report
Please review the email carefully before you click on the button, some key things to look for:
- Don’t trust the display name – A favorite phishing tactic among cybercriminals is to fake the display name of an email.
- Check the links – Hover your mouse over any links in the body of the email. If the link address has numbers or special characters don’t click on it. Check for spelling mistakes – Companies craft their emails carefully. Legitimate messages from companies usually do not have major spelling mistakes or poor grammar.
- Beware of urgent or threatening language in the subject line – Invoking a sense of urgency or fear is a common phishing tactic. Beware of subject lines that claim your “account has been suspended” or your account had an “unauthorized login attempt.”
- Don’t click on attachments – Including attachments that contain viruses and malicious software (malware) is a common phishing tactic. Malware can damage files on your computer, steal your passwords or spy on you without your knowledge. Don’t open any email attachments you weren’t expecting.
Spam & Phishing
Spam
Think of Spam as telemarketing through email. In the same way that you receive those annoying calls at dinner, you can receive those annoying emails at work. Spam runs the full gamut of advertising including home financing, hair loss remedys, or even more embarrassing topics. Try as you may, there is no sure fire solution to getting rid of Spam.
Phishing
Simply put, Phishing is an attempt to defraud the victim. Phishers look to trick users into divulging account information of some sort to gain access and steal what does not belong to them. This is a very creative form of social engineering. Be sure that you really are going to do what you think you’re going to do before you do it.
At Regent University, we utilize several layers of filtering to block spam and phishing messages for university Email. Though these methods improve each day, they still lag behind the technologies that the bad guys employ. For this reason, there isn’t a fool-proof solution to blocking spam or phishing messages. Consider this; on an average day, we block more that 20,000 messages. That’s more than half of the incoming messages we receive each day from Internet addresses. Now imagine how much spam or phishing messages would be in your Inbox if we didn’t have the filters in place.
If you do happen to receive an unsolicited Email message, the best thing to do is just delete it without opening it. For that matter, you shouldn’t open any message you receive that is not of a familiar nature. Instead, you should just delete it from your Inbox.
If you get a message in which the originator is trying to trick you (Phishing), you can report it to helpdesk@regent.edu.
Our filters receive frequent automated updates from the vendor. For this reason, most unsolicited Email is blocked before it gets to your Inbox. However, some messages slip through. Though this means that you may receive the message, it also means that our system is building a profile of the messages and may block subsequent delivery requests. Think of it as ‘taking one for the team’. You may be one that receives the message, but you are passively helping prevent the message from reaching others.
For starters, do you even own such an account? Remember, Phishing is Spam (sent to large groups of people) that tries to get you to reveal personal or financial information. If you disclose such information to the perpetrator, it will most likely lead to fraud or identity theft.
Here are some common themes you may see in Phishing emails or pop-up windows:
– System upgrades or maintenance have caused you password to be changed
– Your account may expire if you don’t change your password
– Your account information has changed, please login and verify the changes
– Phishing messages often contain misspelled words and grammatical errors
Many of these target high-volume accounts such as Ebay, Paypal, bank accounts, and online investment accounts. The common theme is that you must login (give username and password) somewhere and do some action. This information may lead a Phisher to compromise your account and execute fraudulent transactions in their favor.
In an effort to protect your assets, ask yourself questions about the authenticity of such emails. These criminals are skillful in mimicking genuine sites so you are fooled into handing over your account information. If you do receive an email from an entity to which you actually do belong; consider the context of the message. Did you solicit such a message from the entity or is it unexpected? If you ever have any doubts about the authenticity of such messages, don’t hesitate to contact them directly to verify the action they are asking you to take.
Remember, your personal information, accounts, and future are at risk in these Phishing scams. Protect yourself from unnecessary disclosure.
Alerts
There has been a rise in messages that include e-card greetings from unknown users. While Regent’s email security servers are preventing more than 95% of spam and virus activity from reaching Inboxes, there are some messages that pass through. Please be advised that e-card greeting messages are heavily being used to transmit viruses and aim to infect your computer. Please use the following general guidelines when opening email messages.
1. Make sure you are running Antivirus software and that the virus definitions are the most current release.
2. Never open messages with subject lines that do not make sense. Examples include reply indicators without you having sent an email in the first place.
3. Be very wary of messages from people you do not know. While we all have to interact with new people, we generally know the business that transpires between parties. If a message comes through from an unknown person with an illogical subject line, give due consideration prior to opening the message.
4. Delete suspect messages without opening them. Sometimes viruses only need you to open a message in order to infect your computer. To avoid this, don’t open messages you think might cause infection.
If you have and questions or concerns about this or any virus or security threat please contact the Help Desk at 757.352.4076 or helpdesk@regent.edu.
Recently there have been emails sent to our users from a bogus address and are not in any manner affiliated with the Regent University Help Desk or IT department. The following describes the message. However, there could easily be multiple variants of this message.
*********
Sender: regenthelpdesk@hotmail.com
Subject: passwords
Message Body:
Please revert back to original passwords due to some technical difficulties until further notice. Thank you.
Computer Services
*********
If you should receive any message from the IT department or University Help Desk and are unsure of its authenticity, please contact the Help Desk at 757.352.4076 or helpdesk@regent.edu.
The FBI today warned the public to avoid falling victim to an on-going mass email scheme wherein computer users received unsolicited emails purportedly sent by the FBI. These scam emails tell the recipients that their Internet use has been monitored by the FBI and that they have accessed illegal web sites. The emails then direct recipients to open an attachment and answer questions.
The email appears to be sent from the email addresses of mail@fbi.gov and admin@fbi.gov. There may be other similarly styled addresses. The recipient is enticed to open the zip attachment which contains a W32/SOBER.JEN@MM worm. The attachment does not open and its goal is to utilize the recipient’s computer to garner information. Secondly, the virus allows the email to be forwarded to all those listed in the recipient’s address book.
The text of the email is as follows:
********************
Dear Sir/Madam,
We have logged your IP-address on more than 30 illegal Websites.
Important: Please answer our questions! The list of questions are attached.
Yours faithfully,
Steven Allison
Federal Bureau of Investigation-FBI-
935 Pennsylvania Avenue, NW , Room 3220
Washington, DC 20535
Phone: (202) 324-30000
**********************
For more information about this scam visit fbi.gov.
A spam/phishing email message remains in circulation claiming that recipients are eligible for a tax refund from the IRS. The email appears legitimate, but the link included within does not send the user to the IRS website. This reflects typical phishing characteristics and users should remain aware of these types of messages.
The IRS website provides excellent guidance on how to determine fraudulent email. Please read the full details on the Internal Revenue Service’s real website.
When we mention this term, we just don’t mean the physical security that our Public Safety Office provides. In this sense, we mean doing your duties with the mindset of protecting private and confidential information. This doesn’t necessarily mean that you are purposely doing things to disclose private data. You could be doing things that aren’t considered responsible use. Think about it. Do you do enough to ensure that the information you handle from day to day does not fall into the wrong hands or get into the view of wandering eyes? Workplace Security is a concept that we should all subscribe to. Be sure that you do your job protecting all of the information as if it were your own private data.
Well, it’s basically you using the computing systems in the manner for which we provide them to you. When you become a student, faculty, or staff at Regent University, you are permitted to use our computing systems to complete your work and for limited personal use. You are required to become familiar with the Acceptable Use Policy as it provides guidance for what kind of use is and is not permitted on the university’s information systems. If you are a faculty or staff, you’ve already acknowledged that you’ve read and understand the policy. If you’re a student, this policy is included in your student handbook. Either way, you should become familiar with all of the policies that govern information systems use within the university. This will help you understand how to properly utilize our computers and help you to inform others if they are misusing an information system.
Do’s
- Do lock your workstation when you are away from your desk (ctrl + alt + del, then click ‘Lock Computer’)
- Do lock your file cabinets and desk drawers
- Do clean up the files on your desk and place them in a proper secure container
- Do ask questions of those who are seeking information, make sure they really need to know
- Do be alert for people who don’t belong in non-public areas
- Do provide gentle reminders to coworkers when they may need it
- Do double-check your workplace to make sure it is secure before you leave
Dont’s
- Don’t store passwords on your monitor, under your keyboard, or where others may easily find them
- Don’t walk away from your computer while you are still logged in
- Don’t give out more information than is necessary
- Don’t install unnecessary programs on your university owned computer
- Don’t open Email messages if you don’t recognize the sendor or if the subject line is questionable
- Don’t log into a computer so that someone else can use it
- Don’t let anyone connect their personal laptops to the university network
- Don’t leave your portable information assets (laptop, iPod, Palm Pilot, etc.) unattended
If you didn’t create or think of something first, you should be sure to seek licensure or properly credit the bearer of the Intellectual Property rights. We are all somewhat familiar with plagiarism, copyright infringement, trademark violations, patent infringement, and yes, even digital copyright infringement. Though this list is not comprehensive, you get the point. If you have questions about the origin or ownership of something you plan to use, make sure that it’s not already another’s protected work. Even ideas are protected so take care that you don’t use something without properly licensing use, crediting the true source, or violating another’s legal protections.
The Regent University community of teachers and scholars affirms that the biblical principles of truth and honesty are absolutely essential. Indeed, the Bible contains numerous admonitions against false witness, dishonesty and cheating. Upholding the standard of academic integrity with its reliance on honesty is a responsibility of both faculty and students. Conduct that violates academic integrity includes, but is not limited to:
1. Dishonesty. This is lack of integrity exhibited through lying, cheating, defrauding or deceiving. Examples of dishonesty include: copying from the examination paper of another, allowing one’s own examination paper to be copied, reading without the instructor’s consent a copy of the examination prior to the date it is given, giving or receiving unpermitted aid on a take-home examination, class assignment, project and other papers; use of unauthorized aids; submitting the same work product in more than one course without the express permission of the instructor(s); or disclosing or accepting information if one takes a test at a different time than other students in the same course.
2. Plagiarism. This is stealing or using the ideas, writings or images of another as one’s own. It involves failure to acknowledge material copied from others or failure to acknowledge one’s indebtedness to another for the gist of important thoughts in a formal statement, written or oral. Charges of violating academic integrity shall be handled according to established student discipline procedures published in the Catalog and the Student Handbook. (Academic Council, Approved January 1994)
According to Merriam-Webster Online Dictionary, to ‘plagiarize’ means:
- to steal and pass off (the ideas or words of another) as one’s own
- to use (another’s production) without crediting the source
- to commit literary theft
- to present as new and original an idea or product derived from an existing source
At Regent, we have licensed a software application called SafeAssign. This application let’s our staff and faculty evaluate our students’ submissions.
There are many different file sharing applications available for use over the Internet. When you choose to use one of these, be sure that it shares your music, video and other files legally. In most cases, you should be required to pay a fee to ‘swap’ files. An obvious sign that you are violating copyright is if you are not paying to download new files or share files you have already acquired. Examples may include KaZaA, Gnotella, Limewire, and Morpheus.
You should also understand that having these kind of applications on your personal pc may allow other users to connect directly to your pc. This is an extreme security risk. Further, if you install these kind of applications on your University owned workstation or laptop you are violating Regent policy. By allowing others to connect to a Regent workstation or laptop, you expose the University network to unnecessary security risks. As such, violation of this or other University policies may lead.
Not sure what you may and may not do with your university owned computing systems? Read through this policy to see how you can stay in bounds while using your computer. This policy also provides example of misuse so you can stay on the right path.
Because Regent University provides all employees and students with an Electronic Mail (Email) address, we expect our users to abide by this policy. Within it, you will learn what is permissible and what sort of activity you should avoid. It’s true you do have significant leeway when it comes to using your Regent Email account. However, this policy will give you a better perspective regarding appropriate use. Reading and understanding this policy sets you on the right path for sending and receiving Email with your Regent account.
The purpose of this policy is to ensure proper use of Regent University’s Google Workspace for Education systems and make users aware of what Regent University deems acceptable use of these systems. Regent University reserves the right to amend this policy without prior notification at its own discretion.
Privacy and security are no longer an option in our educational system. Security Awareness is essential for everyone’s work habits, both on and off-campus. Regent University is required by several of our accreditation and auditing bodies to have an annually audited Security Awareness Training program with full participation.
So you bring your own laptop to the university? You’ve got temps, contractors, or visitors coming? Be sure you are familiar with the rules that govern who and what may attach to the university’s private networks. We provide a robust wired and wireless public access network for all to use. Make sure that you’re following the guidelines and procedures we recommend so you don’t expose our private network to unnecessary security risks.
The Internet has become a revolutionary tool with regard to social networking and there is no shortage of online brokers that offer a place for all to share information about themselves and become more acquainted with others. Unfortunately, there are predatory individuals on the Internet as well and these persons present a real danger to others. For this reason, Regent University offers this notice in an effort to educate its users of the dangers of such information sharing.
More information about password requirements and secrecy guidelines. We can’t stress the importance of your password. It’s the only thing that separates an intruder from your personal account information. If you’re a faculty or staff at Regent, there’s even more on the line. If an intruder were to compromise your account, it could lead to FERPA violations, HIPAA violations, or other legislative infractions. Learn how to prevent these pitfalls by reading this policy.
Peer to Peer programs are bandwidth hogs and most people don’t even know they have these programs installed. Most peer to peer programs share out copyrighted music and movies which is against the law. This policy breaks down our rules and regulations to protect you and the University.
Regent University provides Antivirus software to all managed workstations and laptops. If you believe your Regent computer does not have Antivirus software on it or the definitions are out-of-date, call the Help Desk immediately.
You should have an Antivirus program running on your personal computers as well. Here is a list of vendors to choose from:
- Fee Based Antivirus Programs
- Free Antivirus Programs
The Federal Trade Commission provides useful Consumer Information on how to protect yourself online.
Symantec Security Response provides detailed information about current threats and how to protect your computer.